On March 11, 2026, Stryker Corporation, one of the giants of medical technology in the U.S., confirmed a "global disruption" of its Microsoft environment following a cyberattack. The public attribution did not come from Washington, but from a group linked to Iran, Handala, which claimed to have extracted 50 terabytes of information and described the operation as a milestone in a "new stage of cyber warfare." The company stated that there were no signs of ransomware or malware and that the incident was contained; however, the reported pattern —inaccessible Windows devices and remote equipment being "erased"— resembles more a destructive attack than a silent theft.
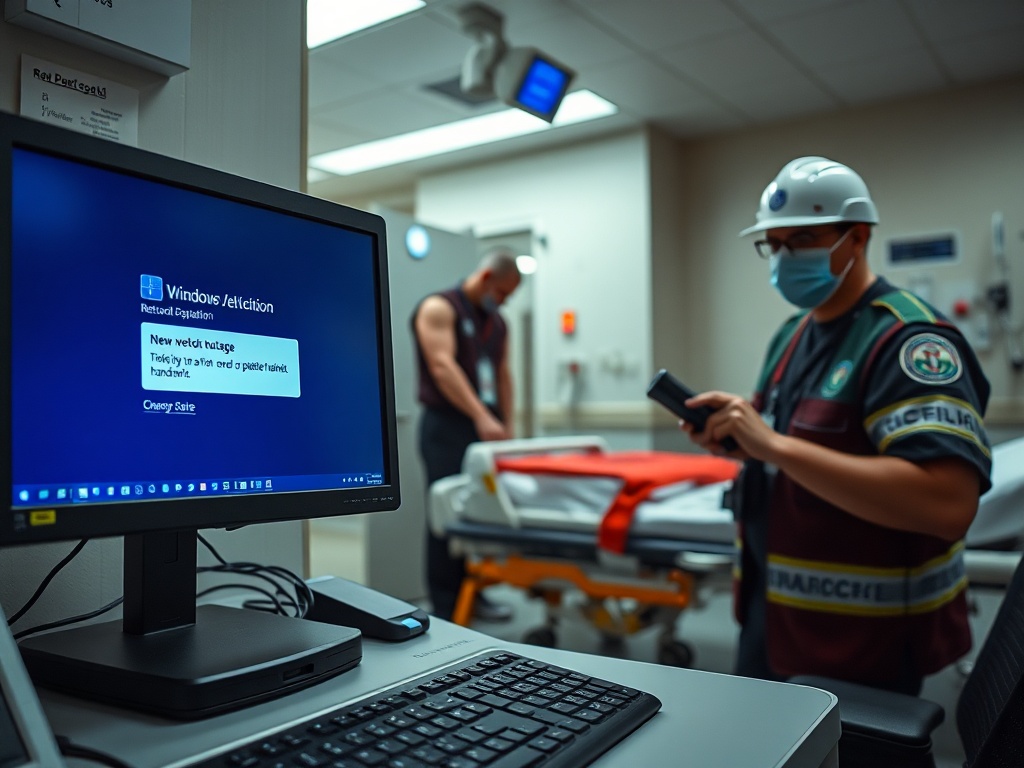
For a manufacturer that reported $25 billion in revenue in 2025 and employs 56,000 people, the cost of a blackout is not merely an IT problem: it is a delivery issue. Stryker does not sell software in the abstract; it sells clinical capability: implants, instruments, hospital beds, surgical robots, defibrillators, and stretchers. And as seen with the fall of Lifenet —a tool for transmitting electrocardiograms used by emergency teams— when digital infrastructure fails, the impact is felt on the front lines, even though local authorities reported no effect on patient care.
The most relevant takeaway for business leaders is the changing nature of risk. We're not just talking about data breaches and fines here; we are discussing coordinated disruption in a geopolitical context of retaliation where the aim could be operational chaos and reputational damage. Stock action reflected this immediately: Stryker's shares fell by more than 3% following initial reports.
A Device Manufacturer with Dependence on Digital Infrastructure
The market often thinks that operational resilience is the domain of "hard" industries like energy or transportation. This case makes it clear that medtech is already critical infrastructure. Stryker operates in a global chain: sales, after-sales, logistics, clinical support, training, technical service, and connected platforms that move sensitive and urgent data. When its "Microsoft environment" experiences global disruption, it’s not just an internal email that goes down; it’s the glue that coordinates people, orders, support, and scaling.
Reports indicate that the disruption began around 0400 GMT on March 11, impacting Windows equipment at multiple locations. In operational terms, this looks like a strike designed to degrade coordination rather than negotiate. This is why the corporate line of "no signs of ransomware" reassures less than it might appear. In a classic extortion attack, the aggressor needs the business to survive long enough to pay. In a destructive or intimidation attack, the return is measured in headlines, customer uncertainty, and political pressure.
The example of Lifenet serves as an uncomfortable reminder: even if medical teams are not "infected," information streams can still break. A state emergency medical services institute in Maryland reported it “non-functional” across much of the state, forcing a return to radio consultations with hospitals. This operational regression translates to minutes, and in emergencies, minutes are inventory that doesn’t get replenished.
From a product perspective, this exposes a typical dependency: critical tools built on a general corporate layer. If the end-user infrastructure is the point of failure, the availability of systems supporting emergencies is tied to decisions and configurations designed for offices, not for clinical continuity.
The 50 Terabyte Figure Changes the Conversation with Clients
Handala claimed to have exfiltrated 50 TB. The number may be part of the theater, but the mere claim is enough to force a new type of business conversation. Unlike an internal incident, here the client does not evaluate whether Stryker "contained" the event. They evaluate whether their supplier can become a vector of exposure for intellectual property, contractual information, technical documentation, or even data associated with the platforms used at the clinical edge.
According to reports, Stryker serves over 150 million patients annually through its equipment. That scale creates an asymmetry: a company can technically contain the incident yet still lose business time due to friction in purchasing, supplier audits, frozen implementations, and security reviews imposed by hospitals and healthcare systems.
In practical terms, the question that arises in procurement is not philosophical. It is concrete: what parts of the service degrade if the supplier loses its corporate network? Continuity is not tested with a press release; it is tested with measurable service levels during a crisis. When a healthcare executive quoted by CNN asked for Stryker to be “more communicative” about the dilemma of whether to disconnect the supplier or not, the point was operational: without actionable information, each hospital is pushed to make defensive decisions that can fragment the installed base.
Here a business pattern emerges: medtech has moved towards revenue and margin supported by digital solutions, connectivity, and services. This increases customer value but also concentrates risk. The damage is not only the week of the incident. It is the erosion of trust that affects renewals, expansions, and consultative sales where security is already part of the tender.
The Innovation that Matters Here is Verifiable Continuity
In large companies, "innovation" often means new product lines, robots, acquisitions, and launches. This case pushes for a less glamorous and more beneficial definition: innovating is designing operations to fail gracefully. When a company declares a business continuity plan activated, the strategic question is whether that continuity was rehearsed with plausible scenarios or if it’s merely a document that only works when the incident is minor.
The available facts suggest a blow to the digital work layer. In that context, useful continuity is the capacity to keep delivering what the customer pays for: deliveries, support, essential telemetry, incident management, and unified communication. If the main channel falls, the plan must have alternative channels already deployed, not improvised. Improvisation during a critical infrastructure crisis does not scale.
My product lens here is simple: the “minimum viable experiment” is not a pilot in a friendly hospital. It is to stress-test, recurrently, the ability to operate with key components out of service. In practical terms, this translates into internal tests simulating loss of identity, loss of corporate devices, loss of emails and ticketing tools, and deliberate degradation of integrations. Not as an annual audit exercise, but as operational evidence that becomes a commercial argument.
It also forces uncomfortable decisions regarding architecture and portfolio. If a platform like Lifenet is critical for emergencies, its dependence on a general corporate network must be justified with availability data or redesigned to operate with greater isolation. That investment is not sold with a slogan; it’s sold with risk reduction for the client and lower probability of contractual interruption for Stryker.
Medtech Enters the Geopolitical Arena with Capital Costs
Reports frame the incident as part of escalating tensions following the onset of a war the previous month, with U.S. and Israeli bombings of Iranian facilities. In that climate, Handala presented the attack as retaliation for an incident in Minab and as a response to cyberattacks against the so-called “Axis of Resistance.” Regardless of the final attribution from U.S. agencies, the economic effect is already materializing: the market adjusts expectations, clients review exposure, and the sector ramps up defensive spending.
There’s a direct consequence for CFOs and boards: capital costs rise when operational risk is perceived as systemic and not idiosyncratic. In sectors where downtime can be associated with healthcare, the tolerance for failure is low. This drives more spending on segmentation, monitoring, response, and redundancy. The cited briefing mentions sector estimates of $10 to $15 billion annually in cybersecurity investment for 2026. The figure, even if debated, marks a direction: medtech is paying the price for having digitized without the same resilience discipline required of other critical sectors.
The competitive game is also shifting. Stryker competes with names like Medtronic and Johnson & Johnson (DePuy Synthes), among others. After an event like this, differentiation will not just be about catalog and price. It will be about demonstrating the capacity to operate under attack and effectively communicate with clients and regulators. Communication is not reputation; it is shared risk management. If a hospital does not know what to disconnect and what to maintain, the provider loses control of the outcome.
The additional note about an unverified alleged attack on Verifone adds a nuance: groups seeking impact can chain narratives, not just intrusions. This amplifies the need for response based on verifiable facts and frequent updates, because the information vacuum is filled with speculation.
The Executive Takeaway is to Measure Resilience as a Product Promise
This episode leaves an operational lesson: in medtech, resilience is no longer a compliance requirement; it is part of the product the customer buys. If the provider touches emergencies, operating rooms, or hospital logistics, their continuity must be demonstrable under adverse conditions. This implies translating cybersecurity into service metrics: what functions are preserved, which degrade, how long recovery takes, how support is maintained, how evidence is protected.
For Stryker, the technical recovery will only be the first leg. The second is commercial: rebuilding trust with concrete information, clear limits, and evidence that continuity processes do not rely on “everything Microsoft working.” The third is strategic: adjusting the design of critical systems so that they do not collapse due to failures in the corporate layer.
The most uncomfortable point for the sector is that destructive attacks do not negotiate. This is why useful innovation is one that reduces the explosion radius and keeps operable the functions that sustain lives and contracts. Sustained business growth occurs when the illusion of the perfect plan is abandoned and constant validation with the real customer is embraced.